mirror of
https://github.com/CVEProject/cvelist.git
synced 2025-08-04 08:44:25 +00:00
"-Synchronized-Data."
This commit is contained in:
parent
22a647d0db
commit
7aab9b2ea8
@ -1,17 +1,76 @@
|
||||
{
|
||||
"data_type": "CVE",
|
||||
"data_format": "MITRE",
|
||||
"data_version": "4.0",
|
||||
"CVE_data_meta": {
|
||||
"ID": "CVE-2022-25377",
|
||||
"ASSIGNER": "cve@mitre.org",
|
||||
"STATE": "RESERVED"
|
||||
"ID": "CVE-2022-25377",
|
||||
"STATE": "PUBLIC"
|
||||
},
|
||||
"affects": {
|
||||
"vendor": {
|
||||
"vendor_data": [
|
||||
{
|
||||
"product": {
|
||||
"product_data": [
|
||||
{
|
||||
"product_name": "n/a",
|
||||
"version": {
|
||||
"version_data": [
|
||||
{
|
||||
"version_value": "n/a"
|
||||
}
|
||||
]
|
||||
}
|
||||
}
|
||||
]
|
||||
},
|
||||
"vendor_name": "n/a"
|
||||
}
|
||||
]
|
||||
}
|
||||
},
|
||||
"data_format": "MITRE",
|
||||
"data_type": "CVE",
|
||||
"data_version": "4.0",
|
||||
"description": {
|
||||
"description_data": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "** RESERVED ** This candidate has been reserved by an organization or individual that will use it when announcing a new security problem. When the candidate has been publicized, the details for this candidate will be provided."
|
||||
"value": "The ACME-challenge endpoint in Appwrite 0.5.0 through 0.12.x before 0.12.2 allows remote attackers to read arbitrary local files via ../ directory traversal. In order to be vulnerable, APP_STORAGE_CERTIFICATES/.well-known/acme-challenge must exist on disk. (This pathname is automatically created if the user chooses to install Let's Encrypt certificates via Appwrite.)"
|
||||
}
|
||||
]
|
||||
},
|
||||
"problemtype": {
|
||||
"problemtype_data": [
|
||||
{
|
||||
"description": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "n/a"
|
||||
}
|
||||
]
|
||||
}
|
||||
]
|
||||
},
|
||||
"references": {
|
||||
"reference_data": [
|
||||
{
|
||||
"url": "https://github.com/appwrite/appwrite/blob/0.12.0/app/controllers/general.php#L539",
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/appwrite/appwrite/blob/0.12.0/app/controllers/general.php#L539"
|
||||
},
|
||||
{
|
||||
"url": "https://github.com/appwrite/appwrite/releases/tag/0.12.2",
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/appwrite/appwrite/releases/tag/0.12.2"
|
||||
},
|
||||
{
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/appwrite/appwrite/pull/2780",
|
||||
"url": "https://github.com/appwrite/appwrite/pull/2780"
|
||||
},
|
||||
{
|
||||
"refsource": "MISC",
|
||||
"name": "https://dubell.io/unauthenticated-lfi-in-appwrite-0.5.0-0.12.1/",
|
||||
"url": "https://dubell.io/unauthenticated-lfi-in-appwrite-0.5.0-0.12.1/"
|
||||
}
|
||||
]
|
||||
}
|
||||
|
||||
18
2024/1xxx/CVE-2024-1805.json
Normal file
18
2024/1xxx/CVE-2024-1805.json
Normal file
@ -0,0 +1,18 @@
|
||||
{
|
||||
"data_type": "CVE",
|
||||
"data_format": "MITRE",
|
||||
"data_version": "4.0",
|
||||
"CVE_data_meta": {
|
||||
"ID": "CVE-2024-1805",
|
||||
"ASSIGNER": "cve@mitre.org",
|
||||
"STATE": "RESERVED"
|
||||
},
|
||||
"description": {
|
||||
"description_data": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "** RESERVED ** This candidate has been reserved by an organization or individual that will use it when announcing a new security problem. When the candidate has been publicized, the details for this candidate will be provided."
|
||||
}
|
||||
]
|
||||
}
|
||||
}
|
||||
18
2024/1xxx/CVE-2024-1806.json
Normal file
18
2024/1xxx/CVE-2024-1806.json
Normal file
@ -0,0 +1,18 @@
|
||||
{
|
||||
"data_type": "CVE",
|
||||
"data_format": "MITRE",
|
||||
"data_version": "4.0",
|
||||
"CVE_data_meta": {
|
||||
"ID": "CVE-2024-1806",
|
||||
"ASSIGNER": "cve@mitre.org",
|
||||
"STATE": "RESERVED"
|
||||
},
|
||||
"description": {
|
||||
"description_data": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "** RESERVED ** This candidate has been reserved by an organization or individual that will use it when announcing a new security problem. When the candidate has been publicized, the details for this candidate will be provided."
|
||||
}
|
||||
]
|
||||
}
|
||||
}
|
||||
18
2024/1xxx/CVE-2024-1807.json
Normal file
18
2024/1xxx/CVE-2024-1807.json
Normal file
@ -0,0 +1,18 @@
|
||||
{
|
||||
"data_type": "CVE",
|
||||
"data_format": "MITRE",
|
||||
"data_version": "4.0",
|
||||
"CVE_data_meta": {
|
||||
"ID": "CVE-2024-1807",
|
||||
"ASSIGNER": "cve@mitre.org",
|
||||
"STATE": "RESERVED"
|
||||
},
|
||||
"description": {
|
||||
"description_data": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "** RESERVED ** This candidate has been reserved by an organization or individual that will use it when announcing a new security problem. When the candidate has been publicized, the details for this candidate will be provided."
|
||||
}
|
||||
]
|
||||
}
|
||||
}
|
||||
@ -1,17 +1,61 @@
|
||||
{
|
||||
"data_type": "CVE",
|
||||
"data_format": "MITRE",
|
||||
"data_version": "4.0",
|
||||
"CVE_data_meta": {
|
||||
"ID": "CVE-2024-25746",
|
||||
"ASSIGNER": "cve@mitre.org",
|
||||
"STATE": "RESERVED"
|
||||
"ID": "CVE-2024-25746",
|
||||
"STATE": "PUBLIC"
|
||||
},
|
||||
"affects": {
|
||||
"vendor": {
|
||||
"vendor_data": [
|
||||
{
|
||||
"product": {
|
||||
"product_data": [
|
||||
{
|
||||
"product_name": "n/a",
|
||||
"version": {
|
||||
"version_data": [
|
||||
{
|
||||
"version_value": "n/a"
|
||||
}
|
||||
]
|
||||
}
|
||||
}
|
||||
]
|
||||
},
|
||||
"vendor_name": "n/a"
|
||||
}
|
||||
]
|
||||
}
|
||||
},
|
||||
"data_format": "MITRE",
|
||||
"data_type": "CVE",
|
||||
"data_version": "4.0",
|
||||
"description": {
|
||||
"description_data": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "** RESERVED ** This candidate has been reserved by an organization or individual that will use it when announcing a new security problem. When the candidate has been publicized, the details for this candidate will be provided."
|
||||
"value": "Stack Based Buffer Overflow vulnerability in Tenda AC9 v.3.0 with firmware version v.15.03.06.42_multi allows a remote attacker to execute arbitrary code via the add_white_node function."
|
||||
}
|
||||
]
|
||||
},
|
||||
"problemtype": {
|
||||
"problemtype_data": [
|
||||
{
|
||||
"description": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "n/a"
|
||||
}
|
||||
]
|
||||
}
|
||||
]
|
||||
},
|
||||
"references": {
|
||||
"reference_data": [
|
||||
{
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/TimeSeg/IOT_CVE/blob/main/tenda/AC9V3/0218/add_white_node.md",
|
||||
"url": "https://github.com/TimeSeg/IOT_CVE/blob/main/tenda/AC9V3/0218/add_white_node.md"
|
||||
}
|
||||
]
|
||||
}
|
||||
|
||||
@ -1,17 +1,100 @@
|
||||
{
|
||||
"data_version": "4.0",
|
||||
"data_type": "CVE",
|
||||
"data_format": "MITRE",
|
||||
"data_version": "4.0",
|
||||
"CVE_data_meta": {
|
||||
"ID": "CVE-2024-26152",
|
||||
"ASSIGNER": "cve@mitre.org",
|
||||
"STATE": "RESERVED"
|
||||
"ASSIGNER": "security-advisories@github.com",
|
||||
"STATE": "PUBLIC"
|
||||
},
|
||||
"description": {
|
||||
"description_data": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "** RESERVED ** This candidate has been reserved by an organization or individual that will use it when announcing a new security problem. When the candidate has been publicized, the details for this candidate will be provided."
|
||||
"value": "### Summary\nOn all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.\n\n### Details\nNeed permission to use the \"data import\" function. This was reproduced on Label Studio 1.10.1.\n\n### PoC\n\n1. Create a project.\n\n\n2. Upload a file containing the payload using the \"Upload Files\" function.\n\n\n\nThe following are the contents of the files used in the PoC\n```\n{\n \"data\": {\n \"prompt\": \"labelstudio universe image\",\n \"images\": [\n {\n \"value\": \"id123#0\",\n \"style\": \"margin: 5px\",\n \"html\": \"<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>\"\n }\n ]\n }\n}\n```\n\n3. Select the text-to-image generation labeling template of Ranking and scoring\n\n\n\n4. Select a task\n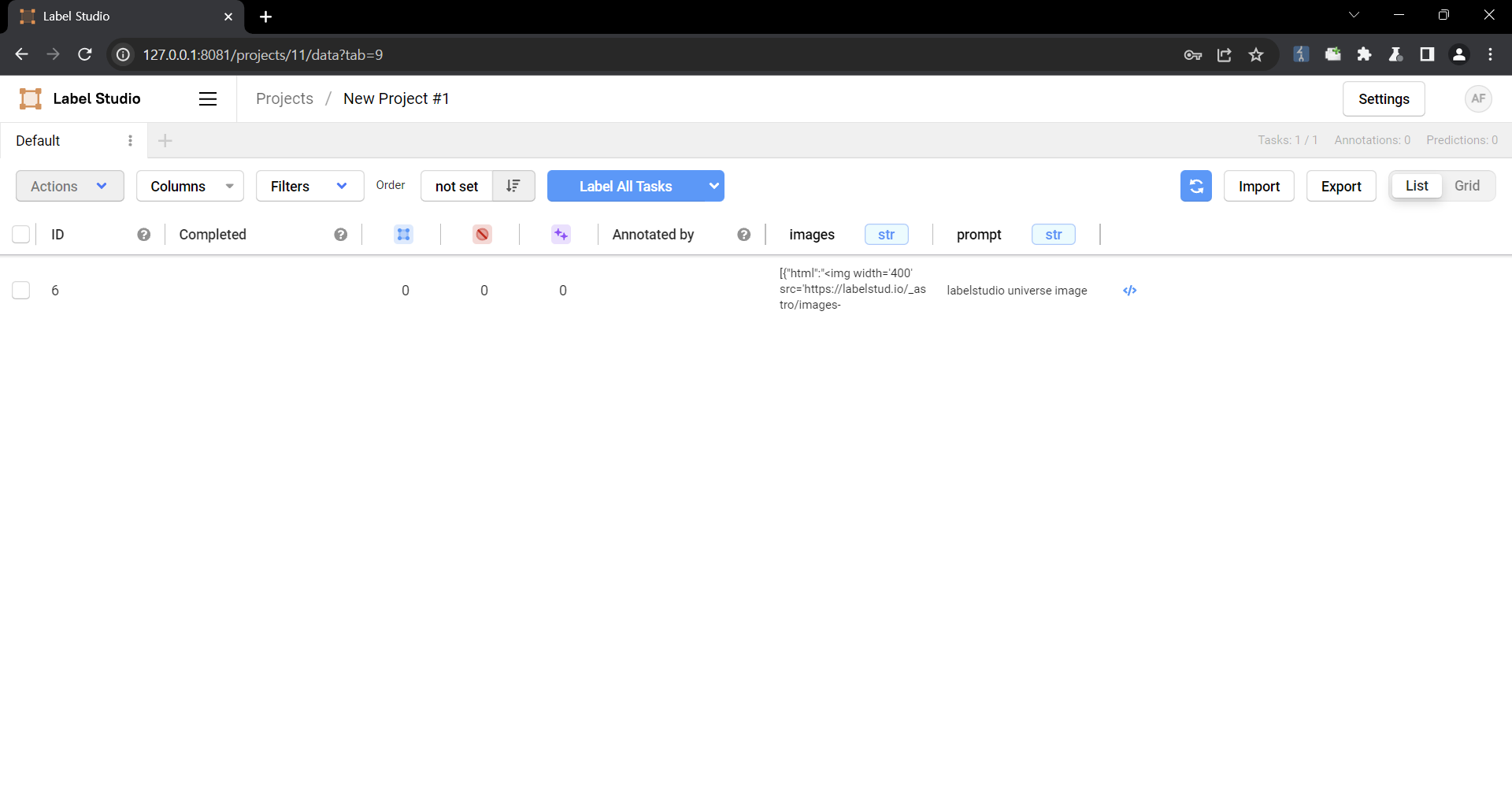\n\n5. Check that the script is running\n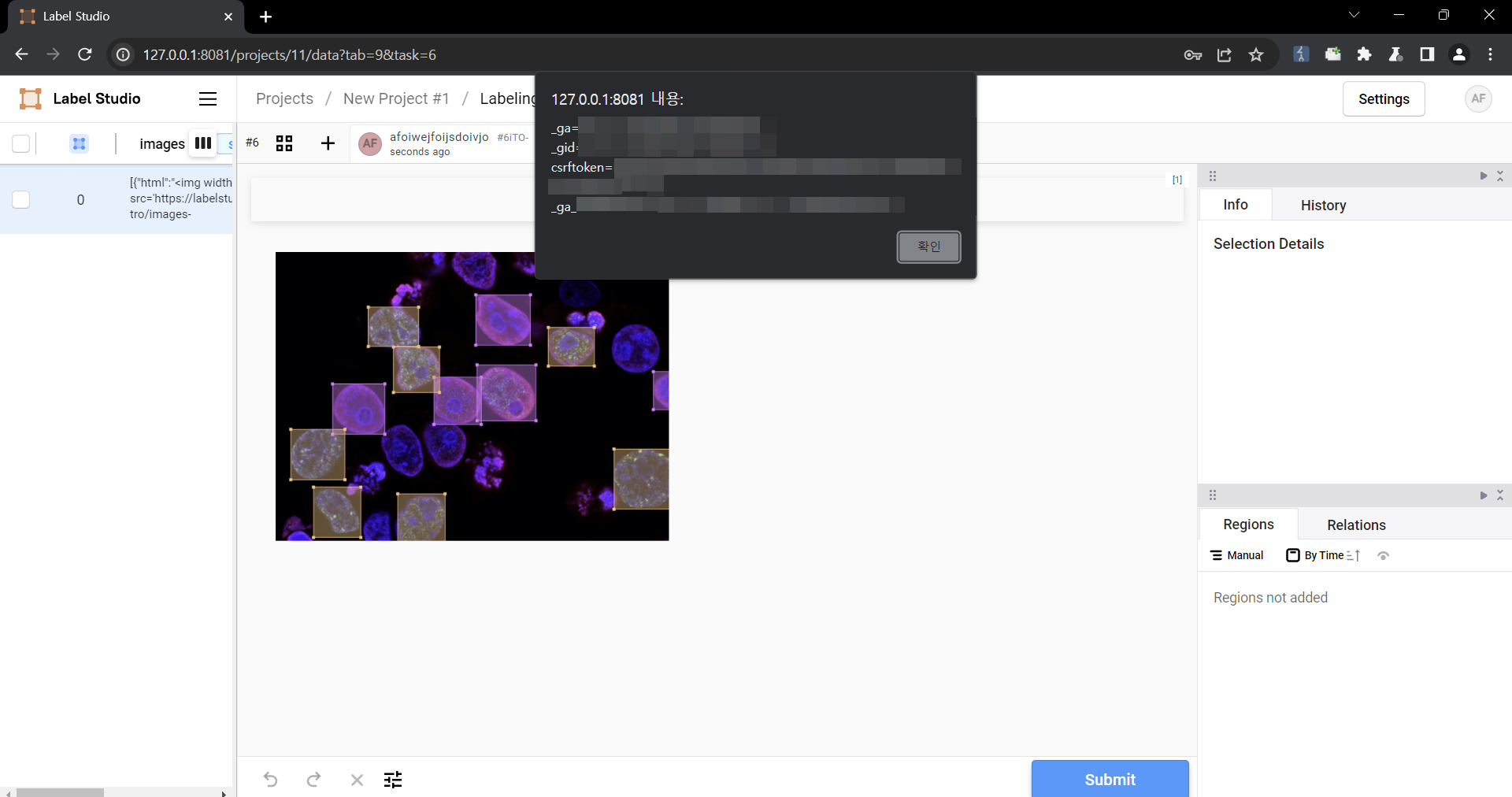\n\n### Impact\nMalicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.\n"
|
||||
}
|
||||
]
|
||||
},
|
||||
"problemtype": {
|
||||
"problemtype_data": [
|
||||
{
|
||||
"description": [
|
||||
{
|
||||
"lang": "eng",
|
||||
"value": "CWE-79: Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')",
|
||||
"cweId": "CWE-79"
|
||||
}
|
||||
]
|
||||
}
|
||||
]
|
||||
},
|
||||
"affects": {
|
||||
"vendor": {
|
||||
"vendor_data": [
|
||||
{
|
||||
"vendor_name": "HumanSignal",
|
||||
"product": {
|
||||
"product_data": [
|
||||
{
|
||||
"product_name": "label-studio",
|
||||
"version": {
|
||||
"version_data": [
|
||||
{
|
||||
"version_affected": "=",
|
||||
"version_value": "< 1.11.0"
|
||||
}
|
||||
]
|
||||
}
|
||||
}
|
||||
]
|
||||
}
|
||||
}
|
||||
]
|
||||
}
|
||||
},
|
||||
"references": {
|
||||
"reference_data": [
|
||||
{
|
||||
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg",
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg"
|
||||
},
|
||||
{
|
||||
"url": "https://github.com/HumanSignal/label-studio/pull/5232",
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/HumanSignal/label-studio/pull/5232"
|
||||
},
|
||||
{
|
||||
"url": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8",
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8"
|
||||
},
|
||||
{
|
||||
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0",
|
||||
"refsource": "MISC",
|
||||
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
|
||||
}
|
||||
]
|
||||
},
|
||||
"source": {
|
||||
"advisory": "GHSA-6xv9-957j-qfhg",
|
||||
"discovery": "UNKNOWN"
|
||||
},
|
||||
"impact": {
|
||||
"cvss": [
|
||||
{
|
||||
"attackComplexity": "LOW",
|
||||
"attackVector": "NETWORK",
|
||||
"availabilityImpact": "NONE",
|
||||
"baseScore": 4.7,
|
||||
"baseSeverity": "MEDIUM",
|
||||
"confidentialityImpact": "LOW",
|
||||
"integrityImpact": "NONE",
|
||||
"privilegesRequired": "NONE",
|
||||
"scope": "CHANGED",
|
||||
"userInteraction": "REQUIRED",
|
||||
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N",
|
||||
"version": "3.1"
|
||||
}
|
||||
]
|
||||
}
|
||||
|
||||
Loading…
x
Reference in New Issue
Block a user